Encrypted messages are under attack: The crypto wars continue.
The German Ministry of the Interior wants to force WhatsApp, Threema and Apple to decrypt encrypted messages. But a backdoor for the "good guys" only is impossible.

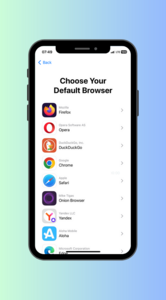
Back in 2014, Germany wanted to become the Encryption Site Number One. Today, the interior ministry has different plans. Seehofer, the German Secretary of the Interior, wants to force encrypted messenger services like WhatsApp, Threema, Signal, Telegram, and Apple's iMessages to decrypt messages for the German authorities upon request.
Longing for decrypted messages like SMS
In the past, authorities could easily get access to plain text information of text messages (SMS) and phone calls from the telecommunication providers. Nowadays, messages - and sometimes even calls - are encrypted when using services like WhatsApp or Signal. The providers don't have access to the encrypted messages - and don't want access.
The authorities claim that criminals, extremists and terrorists would abuse this privacy, and therefore argue that an option to monitor encrypted messages would be necessary. However, the credo that we need more surveillance is wrong. To the contrary, this attempt by Seehofer is just another move in the ongoing crypto wars.
Backdoor for the "good guys" only is impossible
Seehofer pretends with his draft of the new law that it would not be classified as mass surveillance because the authorities would still need a warrant to decrypt encrypted messages of suspected criminals. However, this does not change the fact that Seehofer is asking for a general backdoor, which by definition is a vulnerability.
Cryptography experts around the world conclude that any encryption backdoor destroys online security. Or, as the linked article states: "By demanding backdoors to encryption, Politicians are not asking us to choose between security and privacy. They are asking us to choose no security."
It is general knowledge that any decryption option for state authorities would be a massive security hole that criminals could exploit. For that reason, it is highly unlikely that any encrypted messaging app will include a security hole because of a German law.
No security gained if law passes
Besides, it is highly unlikely that the German Constitutional Court would allow such a privacy-infringing law in the first place as they have declared data retention as unconstitutional multiple times. Obviously, the consequences would not be more security, but less. In the end, such a law would
- signal to users that their apps can't be trusted anymore,
- warn criminals to use different apps,
- lead to an attractive target for (state) hackers - as a backdoor for the "good guys" only does not exist,
- be an example for autocrats, who want to monitor and suppress the opposition.
All this sounds like a very similar fight that Apple had with the US authorities back in 2016. This example shows that companies fight to protect their users' data - and rightly so.
Today, an increasing number of law-abiding citizens understand why protecting their privacy is important, particularly online. No encrypted messaging app will undermine their central promise of security and privacy because of the German Minister Seehofer.
Encryption must remain unbreakable
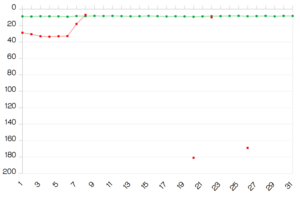
Right now, the situation in Germany is very much in favor of security. Back in 1999, during the first round of the crypto wars, Germany decided in favor of strong encryption. When weighing the interests of the prosecution and the importance of cryptographic tools for the protection and security of German internet users, the German Interior Ministry decided that strong encryption is necessary to protect German citizens and companies from "illegal spying, manipulating and destruction of data". Politicians back then decided that internet users must be protected from spies, hackers and other malicious attackers.
Today, Mr. Seehofer should stop demanding backdoors to encryption, and instead, work hard to make Germany the Encryption Site Number One. After all, this is what his own ministry had promised five years ago.
This draft by the German Interior Minister will not affect the encrypted email service Tutanota. Nevertheless, we will fight this draft from becoming a law because we understand the benefits of strong encryption.