To encrypt or not to encrypt - that's what Danish businesses must decide.
Businesses in Denmark must now protect sensitive personal data in emails with adequate encryption due to a strict interpretation of the GDPR.

Strict interpretation of Article 9 of the European GDPR
The Data Protection Agency in Denmark has made it very clear: With the strict interpretation of Article 9 of the GDPR, Danish companies are required to protect personal data of EU citizens, even when in transit.
As a result, personal data sent via email must be protected with adequate encryption. The Danish Data Protection Agency leaves it to the company to decide whether this encryption must be end-to-end encryption or whether TLS (transport layer encryption) is sufficient:
It is always the data controller who, based on his risk assessment, must assess the level of security that is appropriate. According to the Data Inspectorate, there would be types of processing where encryption with TLS is appropriate and there will be types of treatment where - due to the high level of sensitivity of the personal data - end-to-end encryption will be appropriate.
Tue Goldschmieding, Partner at the Danish law firm Gorissen Federspiel, explains:
Though the Danish Data Protection Agency does not explicitly require end-to-end encryption when sending emails containing special categories of data, the recommendation is very firm and should be interpreted as a defacto requirement.
Let's break down the requirements that the Danish Data Protection Agency has issued to understand this further:
- The Agency says it is up to the Controller of the company to decide whether end-to-end encryption is necessary or not.
- The Controller of the company needs to do a risk assessment.
- This assessment must define how the company makes sure to protect sensitive data in emails adequately.
- The Data Protection Agency said in the above statement that "there will be types of treatment where - due to the high level of sensitivity of the personal data - end-to-end encryption will be appropriate". This tells the companies indirectly that the conclusion of the risk assessment must lead to encrypting emails with sensitive content end-to-end.
Conclusion: Sensitive personal data sent via email must be protected with end-to-end encryption.
While regulators in other European countries might be even less explicit, companies must keep in mind that the Danish regulation is based on the exact same legislation that applies to all European countries: the GDPR.
Learn here how Tutanota focuses on GDPR compliance for emails.
What do Danish companies do to comply with the GDPR requirements?
Many companies are still in the process of enabling methods for end-to-end encrypting their business emails. To this day, there are still companies that rely on TLS encryption only.
However, TLS has a severe weakness that makes relying on it for emails a business risk. With heavy fines of up to 4% of the sales volume in case of a data breach, GDPR compliance for business emails is very important. To fully understand the risk, we need to look at the difference between TLS encryption and end-to-end encryption.
Strict TLS and opportunistic TLS
Strict TLS (HSTS) is a web security policy mechanism that helps to protect websites against protocol downgrade attacks. It allows web servers to declare that web browsers (or other complying user agents) should interact with it using only secure HTTPS connections, and never via the insecure HTTP protocol.
While Strict TLS can easily be added to a website, it is much harder to implement it for emails. The reason is that emails are sent via several servers until they reach their destination. If only one server en-route does not support TLS, an email service with strict TLS could not deliver this email. For that reason, any email service allows emails to arrive to their service, even without strict TLS.
Instead email services use opportunistic TLS where unsuccessful connections fall back to clear text, which does not offer adequate protection in regards to the GDPR.
Two choices for Danish businesses
As a result, Danish businesses have two choices: They can either host their emails themselves, applying strict TLS while accepting that some emails will never reach them because their server does not accept emails that were sent in the clear, without proper TLS protection.
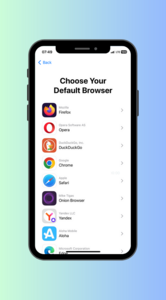
Alternatively, Danish businesses can use an email service which offers end-to-end encryption. This way, they can easily encrypt any email containing sensitive personal data end-to-end, and still accept general emails that were sent in the clear, without proper TLS protection.
Benefits of end-to-end encryption
End-to-end encryption in emails makes sure that only the intended recipient has the key to decrypt the email. It cannot be read by anybody else because the email content is unreadable data even if intercepted while in transit.
When the recipients receive an end-to-end encrypted email, they need to use their private key (asymmetric encryption) or a password (symmetric encryption) to decrypt the data and transform it back into a readable format.
In contrast to transport layer encryption (TLS), end-to-end encryption fully protects a message while in transit as well as after it has been received by the recipient’s inbox. This means that any third party who has access to this email or is able to intercept it will only see the encrypted version of the email and cannot decipher its content.
GDPR compliance in emails
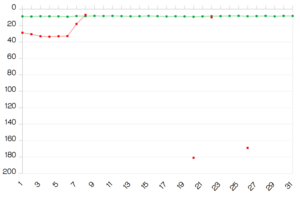
The new Danish requirement for email encryption should be viewed as a competitive advantage – not a hindrance. After all, it will not be surprising if countries outside of the European Union will follow the GDPR example. Email encryption is on the rise, not just among Tutanota users, but everywhere in the world.
Danish authorities are being serious about encryption
This January the Data Protection Agency has published their half year plan that specifies the inspection's focus during the first half of 2019.
- Breach of personal data security by public authorities and private companies
- The Data Protection Advisor function of the municipalities
- Encryption of emails from private companies
- Authorization of employees at the municipalities
- It registered the right of insight with public authorities and private companies
- Use (and reuse) of data in the municipal administration
- Aggregation and compilation of data for use by resellers at private companies
This plan shows that the Data Protection Agency is being serious about their requirements that Danish businesses must protect sensitive data in emails with adequate encryption. The advocate Tue Goldschmieding said:
The Agency is particularly targeting law firms and accountants with this upcoming inspection. These companies need to communicate sensitive information via email with their clients on a day-to-day basis, and must make sure that the data is properly protected.
How does this affect companies in other countries?
Denmark is not explicitly requiring encryption of emails with sensitive personal information, but the statements from the Danish Data Protection Agency leave no room for interpretation, according to Tue Goldschmieding:
The Agency does not point their fingers at companies saying 'You must encrypt'. But the way the Agency is explaining how sensitive data should be protected in transit can only lead to one conclusion of a company's risk assessment: That emails containing sensitive personal data must be protected with encryption. And end-to-end encryption is obviously the best choice - if not the only one.
While other European countries are even less explicit in their requirements, any company must keep in mind that the same legislation - the European GDPR - is the basis of the Danish requirement towards encrypting emails containing sensitive personal data.
In this regards, any company doing business in Europe or with European citizens should take proactive measures by implementing an easy way of encrypting emails with sensitive content.
Secure your business emails with Tutanota
Tutanota focuses on offering secure email that lets your employees easily encrypt any email to any recipient end-to-end. By combining the advantages of the cloud – availability, automatic back-up, auto-sync, cost-efficiency – with the advantages of hosting your emails on your local server – security and data sovereignty, your business can save time and money when switching to Tutanota.
This combination makes Tutanota the perfect secure email service for businesses.